Recently I am fortunate to be introduced of a wonderful book about self improvement. As a Kindle user, the first thing I do is to look for it in the Kindle Store. Bummer, the search result returns nothing. Having checked again with my friend, the book was bought at Kobo. That’s not good, because I prefer reading books on my e-ink Kindle device rather than on LCD or LED screens, since I would suffer from eye strain easily after prolonged reading using them. Seems as I am getting older my eyes are becoming more sensitive to strong visible lights.
I have no experience with Kobo before, so I did some research, found that Kobo’s e-books are not compatible with Kindle. The book that I want is in EPub format with DRM protection (bad!), Kindle doesn’t take ePub, let alone DRM-protected ones.
I have no other choice, except to find my way to decrypt the e-book to remove the DRM. Once it is DRM-free, I can simply convert it from EPub to MOBI/AWZ3, which is natively supported by Kindle.
As my main working machine is Ubuntu, what I am going to write are only applicable to Ubuntu. With some tweaking you can achieve the same result on other Linux distributions. I performed all the steps under Ubuntu 19.04. The process is a bit tricky but not impossible. It mainly involves these steps:
- Use Adobe digital editions under WINE to save Kobo e-book as a DRM-encrypted ePUB file.
- Use DeDRM plugin in Calibre to remove DRM from the EPUB file.
- Convert the DRM-free EPUB to MOBI/AWZ3 by Calibre.
Save the e-book into DRM-encrypted EPUB
- First login to Kobo and download the e-book’s ACSM file. ACSM a very small descriptive file that contains metadata of your e-book.
- Go to your books library in Kobo, under the book cover there is an icon with 3 dots. Click on it and it will display a menu, the third item is “Download”. Click on it, the website will prompt you to download a file, its filename ends with “.acsm”. Save it for later use.

- First login to Kobo and download the e-book’s ACSM file. ACSM a very small descriptive file that contains metadata of your e-book.
- Go to your books library in Kobo, under the book cover there is an icon with 3 dots. Click on it and it will display a menu, the third item is “Download”. Click on it, the website will prompt you to download a file, its filename ends with “.acsm”. Save it for later use.
- If you do not have WINE installed, install it with other tools by:
sudo apt install wine-stable winetricks cabextract - Now download Adobe digital editions (ADE) version 2.0 and install it in WINE ADE 2.0 is available at http://download.adobe.com/pub/adobe/digitaleditions/ADE_2.0_Installer.exe, download it for later use.
- Run the following commands:
1234export WINEARCH=win32export WINEPREFIX=~/.wine-kobowinetricks -q dotnet35sp1 corefonts windowscodecswine ADE_2.0_Installer.exe # follow the normal installation procedure.
- In ADE, open the acsm file by going to
File > Add to Library(or pressCtrl-O). There is a GUI glitch that the menu is not shown when you click “File” until you move your mouse around. - ADE will ask you to “Authorize Your Computer”. If you do not have an Adobe ID, click on the “Create an Adobe ID” link, and you will be brought to a web page, where you can sign up. If you already have an Adobe ID, sign in with your existing Adobe ID and password.
- Voila! After you have signed in, ADE will start loading your e-book. After awhile, your e-book will be shown in ADE. Now, check your
~/Documents/My Digital Editionsfolder, you should see your e-book there in EPUB format!
Remove DRM from Your E-Book
- If you do not have Calibre in your computer, install it with
apt install calibre. - Then you need to import the DeDRM plugin to Calibre, as Calibre doesn’t come with the capability to remove DRM out of the box.
- Go to https://github.com/apprenticeharper/DeDRM_tools/releases, and download the latest DeDRM_tools zip file.
- Unzip it. There are many files but what we care is the
DeDRM_calibre_pluginfolder.
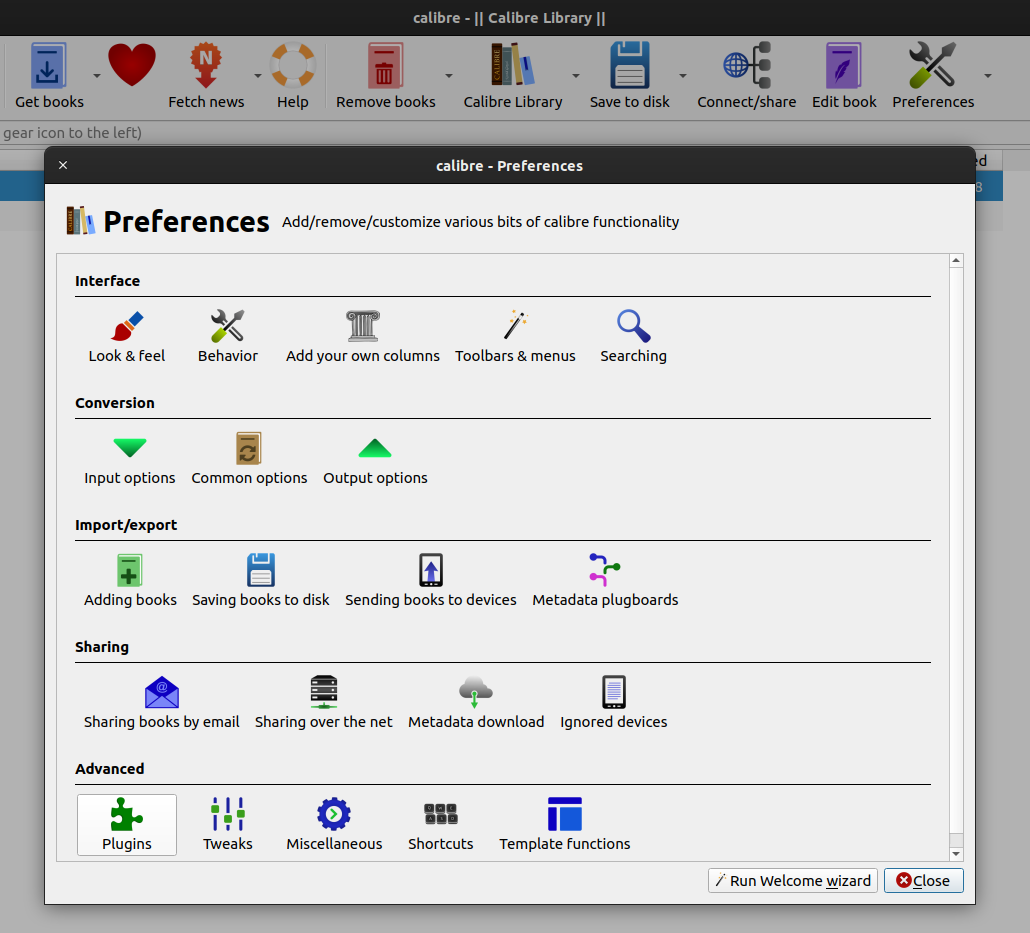
12$ ls DeDRM_calibre_plugin/DeDRM_plugin_ReadMe.txt DeDRM_plugin.zip - Open up Calibre, click on the Preferences icon at the top bar. From there, locate the Plugins icon under the “Advanced” heading. In my Calibre it is the last row.
Calibre Preferences dialog - At the very bottom of the plugins window, there is a button called “Load plugin from file”. Click on it. Browse to the Calibre plugin folder that you extracted from the zip file, select DeDRM_plugin.zip within that folder. Calibre will warn you that importing an external plugin is a potential security risk. That’s fine, just confirm your choice. Once it is done, Calibre will show you a success message telling you to restart the program for the changes to take effect. Do as you are told.
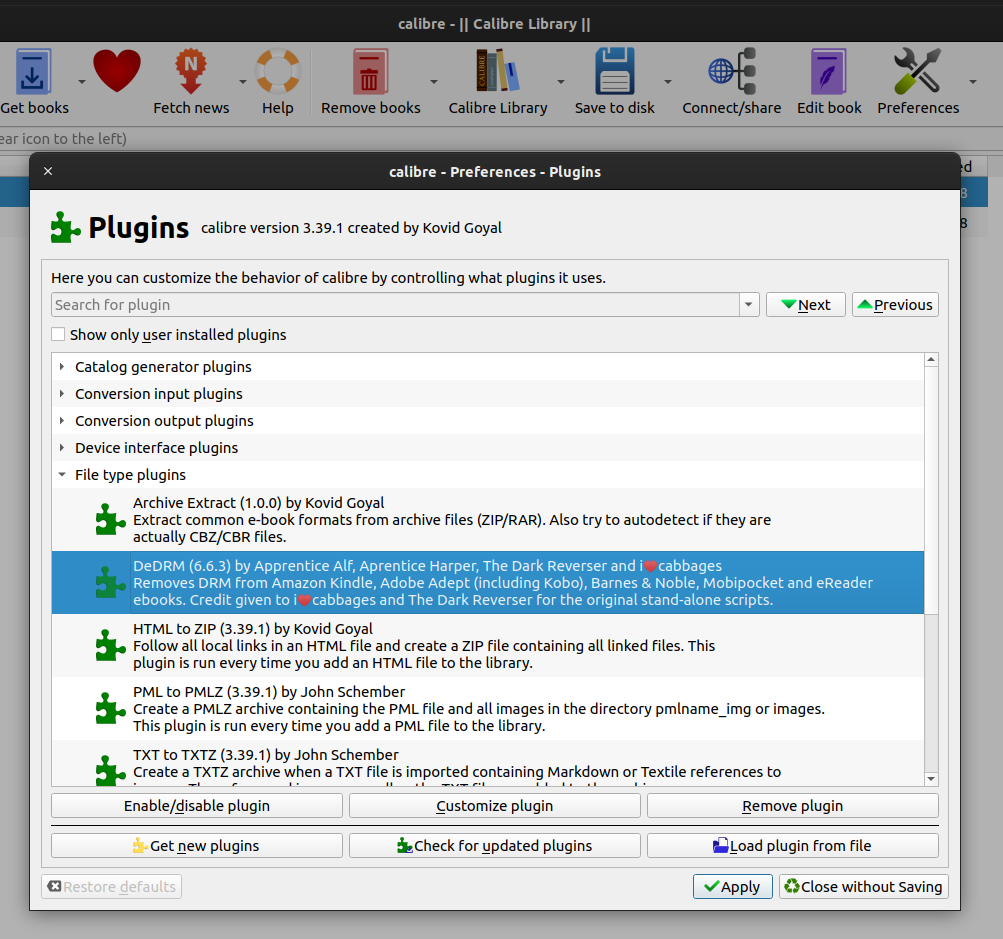
DeDRM plugin installed
- Now fire up Calibre again. Click on “Add books” icon on the top bar. Choose the EPUB e-book from
~/Documents/My Digital Editions. Your e-book will be shown in the main window. Click on the “View” icon in the top bar, you should now be able to view it! If you can’t view it saying that the book is encrypted, you may have done something wrong in importing the DeDRM plugin. Go back and check that the plugin is properly installed.
Convert the DRM-free EPUB to MOBI/AWZ3
- Since you now have your e-book unencrypted, you can convert the e-book to any format that you desire. If you are like me and prefer Kindle, you should convert it to AWZ3.
- Select your e-book in the main window, then click on the “Convert books” icon that is on the top bar.
- A new window will show up for configuring many conversion settings. Since we are converting for Kindle, choose “AZW3” as the “Output format” at the top right corner of the window. Then click on “Page setup” in the left pane, choose an “Output profile” for your device. There are many different settings that you can test with. Once you are satisfied, click “OK”. Calibre will now start converting your e-book to AZW3, wait for a while, it will prompt you when it is done.
- After the conversion completes, look at the right hand side of the main window. You can see the label “Path” under the book cover, after “Path” there is a link called “Click to open”. Click on it, your file browser will open and you should see a new file with the extension azw3. That is the file that you can import to your Amazon Kindle. Transfer it to your Kindle device just like any other Kindle e-books. Enjoy!
